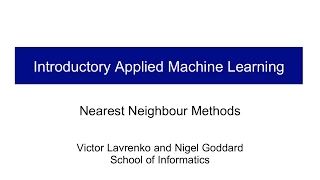
From playlist k-Nearest Neighbor Algorithm

An informal introduction to cryptography. Part of a larger series teaching programming at http://codeschool.org
From playlist Cryptography
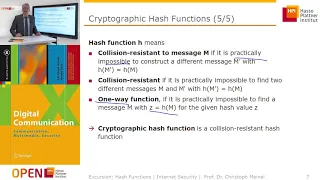
Cryptographic Hash Functions: Part 1
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
Cryptographic Hash Functions: Part 2
Cryptographic Hash Functions Applications of Crypto Hash Functions Birthday Problem Secure Hash Algorithm (SHA)
From playlist Network Security

Clustering (3): K-Means Clustering
The K-Means clustering algorithm. Includes derivation as coordinate descent on a squared error cost function, some initialization techniques, and using a complexity penalty to determine the number of clusters.
From playlist cs273a

Recitation 24: Final Exam Review
MIT 6.006 Introduction to Algorithms, Fall 2011 View the complete course: http://ocw.mit.edu/6-006F11 Instructor: Victor Costan License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.006 Introduction to Algorithms, Fall 2011

Hashing And EKE Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Nexus Trimester - Graham Cormode (University of Warwick) 1/2
Stream, sketching and Big Data - 1/2 Graham Cormode (University of Warwick) 1/2 March 08, 2016 Abstract: A fundamental challenge in processing the massive quantities of information generated by modern applications is in extracting suitable representations of the data that can be stored, m
From playlist 2016-T1 - Nexus of Information and Computation Theory - CEB Trimester
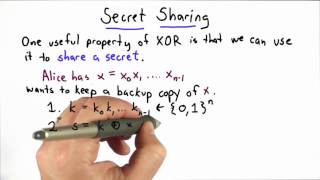
Secret Sharing - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Sparsifying and Derandomizing the Johnson-Lindenstrauss Transform - Jelani Nelson
Jelani Nelson Massachusetts Institute of Technology January 31, 2011 The Johnson-Lindenstrauss lemma states that for any n points in Euclidean space and error parameter 0 less than eps less than 1/2, there exists an embedding into k = O(eps^{-2} * log n) dimensional Euclidean space so that
From playlist Mathematics

Private Algorithms with Minimal Space
A Google TechTalk, 2020/7/29, presented by Adam Smith, Boston University ABSTRACT: We show that a classic algorithm for counting distinct elements in small space is differentially private with only small modifications. The result is an algorithm with the same space guarantee as in the nonp
From playlist 2020 Google Workshop on Federated Learning and Analytics
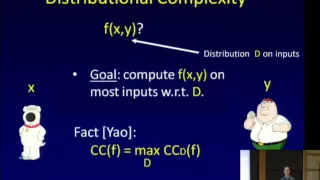
Compressing Bounded-Round Communication - Mark Braverman
Mark Braverman Microsoft Research New England April 6, 2010 In this talk we will present a near-optimal compression scheme for bounded-round randomized 2-party communication protocols. Previously, such a scheme was only known for protocols where the inputs to the parties are independent. T
From playlist Mathematics

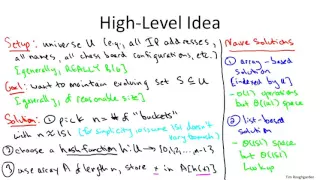
Lec 7 | MIT 6.046J / 18.410J Introduction to Algorithms (SMA 5503), Fall 2005
Lecture 07: Hashing, Hash Functions View the complete course at: http://ocw.mit.edu/6-046JF05 License: Creative Commons BY-NC-SA More information at http://ocw.mit.edu/terms More courses at http://ocw.mit.edu
From playlist MIT 6.046J / 18.410J Introduction to Algorithms (SMA 5503),

CERIAS Security: Integrity for Outsourced Content Publishing and Database Queries 3/6
Clip 3/6 Speaker: Danfeng Yao · Brown University In outsourced content publishing, the data owner gives the content to a service provider who answers requests from users. Similarly, in outsourced databases, the data owner delegates a service provider to answer queries. Outsourcing ena
From playlist The CERIAS Security Seminars 2006