What Is System Identification? | System Identification, Part 1
Get an introduction to system identification that covers what it is and where it fits in the bigger picture. See how the combination of data-driven methods and physical intuition can improve the model with so-called grey-box methods. Watch the full series on System Identification: https:
From playlist System Identification

Online and Recursive System Identification | System Identification, Part 4
Online system identification algorithms estimate the parameters and states of a model as new data is measured and available in real-time or near real-time. Brian Douglas covers what online system identification is, why it’s a good option for real-time situations, and the general ideas beh
From playlist System Identification

Linear System Identification | System Identification, Part 2
Learn how to use system identification to fit and validate a linear model to data that has been corrupted by noise and external disturbances. Watch the full series on System Identification: https://youtube.com/playlist?list=PLn8PRpmsu08p5KkY8_P8G6fJhelUHHi6b Noise and disturbances can m
From playlist System Identification
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security
Fundamental concepts of intrusion detection are discussed. Various types of intrusion are analyzed. Password management is explained.
From playlist Network Security

Nonlinear System Identification | System Identification, Part 3
Learn about nonlinear system identification by walking through one of the many possible model options: A nonlinear ARX model. Watch the full series on System Identification: https://youtube.com/playlist?list=PLn8PRpmsu08p5KkY8_P8G6fJhelUHHi6b Brian Douglas covers the importance of adding
From playlist System Identification

How to Perform System Identification of Blue Robotics Thrusters
This video will show you how to use the System Identification app to create linear mathematical models of a component with the Blue Robotics T200 thruster as an example. System Identification is a data driven approach to developing mathematical models for components or systems. You will le
From playlist “How To” with MATLAB and Simulink
System Design: How to store passwords in the database?
Weekly system design newsletter: https://bit.ly/3tfAlYD Checkout our bestselling System Design Interview books: Volume 1: https://amzn.to/3Ou7gkd Volume 2: https://amzn.to/3HqGozy Other things we made: Digital version of System Design Interview books: https://bit.ly/3mlDSk9 Twitter: htt
From playlist Computer Science Fundamentals

Introduction to System Identification Toolbox
Get a Free Trial: https://goo.gl/C2Y9A5 Get Pricing Info: https://goo.gl/kDvGHt Ready to Buy: https://goo.gl/vsIeA5 Get started with System Identification Toolbox. For more videos, visit http://www.mathworks.com/products/sysid/examples.html
From playlist Control System Design and Analysis
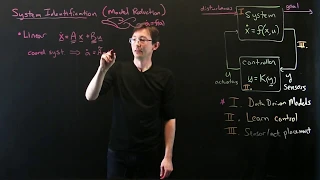
Data-Driven Control: Linear System Identification
Overview lecture on linear system identification and model reduction. This lecture discusses how we obtain reduced-order models from data that optimally capture input--output dynamics. https://www.eigensteve.com/
From playlist Data-Driven Control with Machine Learning

Biometrics for identification – What do practitioners need, and what can government do?
Harry Farmer, Researcher, Ada Lovelace Institute Biometric technologies, from facial recognition to digital fingerprinting, have proliferated through society in recent years. Benefits are often counterbalanced by ethical and societal concerns. These worries compound a growing controversy
From playlist Turing trustworthy digital identity conference

Lennart Ljung on System Identification Toolbox: History and Development
Get a Free Trial: https://goo.gl/C2Y9A5 Get Pricing Info: https://goo.gl/kDvGHt Ready to Buy: https://goo.gl/vsIeA5 Professor Lennart Ljung describes how he developed System Identification Toolbox™ and why he chose to write it in MATLAB®. For more videos about System Identification Tool
From playlist Lennart Ljung on System Identification

Lennart Ljung on the Past, Present, and Future of System Identification
Get a Free Trial: https://goo.gl/C2Y9A5 Get Pricing Info: https://goo.gl/kDvGHt Ready to Buy: https://goo.gl/vsIeA5 Professor Lennart Ljung talks about where system identification started and where it is headed. For more videos about System Identification Toolbox, visit: http://www.math
From playlist Lennart Ljung on System Identification

Lennart Ljung on System Identification Toolbox: Advice for Beginners
Get a Free Trial: https://goo.gl/C2Y9A5 Get Pricing Info: https://goo.gl/kDvGHt Ready to Buy: https://goo.gl/vsIeA5 Professor Lennart Ljung, creator of System Identification Toolbox™, offers advice on how to get started. For more videos about System Identification Toolbox, visit: http:/
From playlist Lennart Ljung on System Identification

3 Ways to Build a Model for Control System Design | Understanding PID Control, Part 5
Tuning a PID controller requires that you have a representation of the system you’re trying to control. This could be the physical hardware or a mathematical representation of that hardware. If you have physical hardware, you could guess at some PID gains, run a test to see how it perfor
From playlist Understanding PID Control

Speaker: Nicholas Bentley A new approach to copyright in the digital world A discussion of the Intellectual Contributions model and the Rights Office system as an alternative for regulating copyright in a digital environment. For more information visit: http://bit.ly/22c3_information To
From playlist 22C3: Private Investigations

How To Choose The Right Database?
Weekly system design newsletter: https://bit.ly/3tfAlYD Checkout our bestselling System Design Interview books: Volume 1: https://amzn.to/3Ou7gkd Volume 2: https://amzn.to/3HqGozy Other things we made: Digital version of System Design Interview books: https://bit.ly/3mlDSk9 Twitter: htt
From playlist Database

Jean-Christophe Loiseau: "Chaotic convection and Lorenz-like dynamics/A brief overview of SINDy"
Machine Learning for Physics and the Physics of Learning 2019 Workshop III: Validation and Guarantees in Learning Physical Models: from Patterns to Governing Equations to Laws of Nature "Chaotic convection and Lorenz-like dynamics/A brief overview of SINDy" Jean-Christophe Loiseau - École
From playlist Machine Learning for Physics and the Physics of Learning 2019
