Summary - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
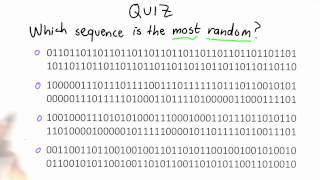
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

The Diagonalization of Matrices
This video explains the process of diagonalization of a matrix.
From playlist The Diagonalization of Matrices

Symmetric matrices - eigenvalues & eigenvectors
Free ebook http://tinyurl.com/EngMathYT A basic introduction to symmetric matrices and their properties, including eigenvalues and eigenvectors. Several examples are presented to illustrate the ideas. Symmetric matrices enjoy interesting applications to quadratic forms.
From playlist Engineering Mathematics
We have already looked at the column view of a matrix. In this video lecture I want to expand on this topic to show you that each matrix has a column space. If a matrix is part of a linear system then a linear combination of the columns creates a column space. The vector created by the
From playlist Introducing linear algebra

Ex: Multiplying Fractions Using Pattern Blocks
This video explains how to use pattern blocks to determine the product of two fractions. Site: http://mathispower4u.com
From playlist Multiplication and Division of Mixed Numbers

Randomness Quiz Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Jamovi 1.2/1.6 Tutorial: Randomizer Module (Episode 22)
In this Jamovi tutorial, I go through the Randomizer module/package inside jamovi. This module is an additional one that can be added to the base program. It is designed to help with the cumbersome task of making randomized conditions in either a between-subjects or within-subjects design.
From playlist Jamovi Tutorials

Live CEOing Ep 664: Language Design in Wolfram Language [Design of Symbols]
In this episode of Live CEOing, Stephen Wolfram discusses upcoming improvements and features to the Wolfram Language. If you'd like to contribute to the discussion in future episodes, you can participate through this YouTube channel or through the official Twitch channel of Stephen Wolfram
From playlist Behind the Scenes in Real-Life Software Design

I finish my lecture on Experimental Design with an introduction to Block Design, Matched Pairs Design, and Double Blind Experiments. Check out http://www.ProfRobBob.com, there you will find my lessons organized by class/subject and then by topics within each class. Find free review test,
From playlist AP Statistics
What is counterbalancing? | Research Methods w/ Dr. Swan
This video is the video on demand (VOD) from my Twitch livestream. There are likely several edits for flow and topic. No facecam or overlays from stream appear in this video. Video contains only Microsoft OneNote information. Topic for this stream: I discuss how to counterbalance with-gro
From playlist Research Methods

3. Blockchain Basics & Cryptography
MIT 15.S12 Blockchain and Money, Fall 2018 Instructor: Prof. Gary Gensler View the complete course: https://ocw.mit.edu/15-S12F18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP63UUkfL0onkxF6MYgVa04Fn In this lecture, Prof. Gensler, explains the basics of blockchain an
From playlist MIT 15.S12 Blockchain and Money, Fall 2018

Top Hashing Algorithms In Cryptography | MD5 and SHA 256 Algorithms Explained | Simplilearn
In this video on Top Hashing Algorithms In Cryptography, we will cover the technical aspects of hashing while going through some well-known hash functions and algorithms at the end. We cover the basics of cryptography and its applications. We also have detailed MD5 and SHA265 Explained sec
From playlist Cyber Security Playlist [2023 Updated]🔥

On the symmetries of and equivalence test for design polynomials by Nikhil Gupta
Discussion Meeting Workshop on Algebraic Complexity Theory  ORGANIZERS Prahladh Harsha, Ramprasad Saptharishi and Srikanth Srinivasan DATE & TIME 25 March 2019 to 29 March 2019 VENUE Madhava Lecture Hall, ICTS Bangalore Algebraic complexity aims at understanding the computationa
From playlist Workshop on Algebraic Complexity Theory 2019

Cyber Security Week Day - 1 |Cryptography Full Course | Cryptography & Network Security| Simplilearn
🔥Advanced Executive Program In Cybersecurity: https://www.simplilearn.com/pgp-advanced-executive-program-in-cyber-security 🔥Caltech Cybersecurity Bootcamp(US Only): https://www.simplilearn.com/cybersecurity-bootcamp This video on Cryptography full course will acquaint you with cryptograph
From playlist Simplilearn Live
Pierre Liardet - Randomness and Cryptography with a dynamical point of view (Part 2)
Randomness and Cryptography with a dynamical point of view (Part 2)
From playlist École d’été 2013 - Théorie des nombres et dynamique

Ruby Conf 2013 - Being Boring: A Survival Guide to Ruby Cryptography
We all know that security is hard, and that math is hard, but what happens when you put them together? Cryptography is an increasingly essential tool for building secure systems, but also a perilous minefield where any number of mistakes can lead to insecure systems. This talk will take y
From playlist Ruby Conf 2013 - Miami Beach, FL