
Symmetric Key Cryptography: The Keyword Cipher
This is the second in a series about cryptography; an extremely important aspect of computer science and cyber security. It covers a substitution cipher called the keyword cipher, also known as the Vigenère cipher. It explains how a keyword, or key phrase, can be used to effectively gene
From playlist Cryptography

From playlist Week 2 2015 Shorts

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

Symmetric Key Cryptography: The Caesar Cipher
This is the first in a series about cryptography; an extremely important aspect of computer science and cyber security. It introduces symmetric key cryptography with a well known substitution cipher, namely the Caesar Cipher. It includes a few examples you can try for yourself using diff
From playlist Cryptography

From playlist Week 2 2015 Shorts

Squaring The Circle (feat. James Grime) - Objectivity 171
Dr James Grime joins us at The Royal Society to look at all manner of things from secret codes to fancy objects... More links below ↓↓↓ Featuring Dr James Grime speaking with Brady and Keith Moore. Accompanying documents: http://www.bradyharanblog.com/blog/squaring-the-circle-the-documen
From playlist James Grime on Numberphile

I know Kung Fu! (or neo4j on Rails without jRuby)
"Reality is a graph, embrace it!" Sure graph databases are really cool and have a timestamp dated next week, but do you know when you should actually use one? Sometimes living on the bleeding edge pays off and in this talk, I'll show you how you can simplify your application and model your
From playlist Cascadia Ruby 2012
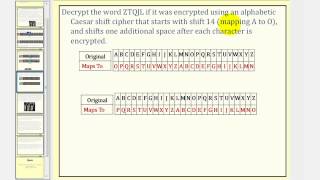
Cryptography: Caesar Cipher With Shift
This lesson explains how to encrypt and decrypt a message using Caeser cipher with a shift. Site: http://mathispower4u.com
From playlist Cryptography

This video is about the Vigenere Cipher: years used, key format, encryption. Note: sorry, I may have mispronounced names. Decryption (known key): http://youtu.be/oHcJ4QLiiP8 Decryption (unknown key): http://youtu.be/LaWp_Kq0cKs
From playlist Cryptography and Coding Theory

Vigenere Cipher - Decryption (Known Key)
This video shows how to decrypt the ciphertext when the key is known. Decryption (unknown key): http://youtu.be/LaWp_Kq0cKs Encryption: http://youtu.be/izFivfLjD5E
From playlist Cryptography and Coding Theory

We need to talk... about fractals!
So yeah. Fractal trees are hard to make. We did what we could. -- Watch live at https://www.twitch.tv/simuleios
From playlist Fractal

Visual telegraphs (case study) | Computer Science | Khan Academy
The history of visual telegraphs Watch the next lesson: https://www.khanacademy.org/computing/computer-science/informationtheory/info-theory/v/history-of-static-electricity-language-of-coins-6-12?utm_source=YT&utm_medium=Desc&utm_campaign=computerscience Missed the previous lesson? https
From playlist Journey into information theory | Computer Science | Khan Academy

Alexander Beilinson - Height pairing and vanishing cycles
Correction: The affiliation of Lei Fu is Tsinghua University.
From playlist Conférence « Géométrie arithmétique en l’honneur de Luc Illusie » - 5 mai 2021

From playlist CS50 Walkthroughs (Problem Sets)

From playlist CS50 Sections 2012

ADFGVX Cipher: Encryption and Decryption (Updated)
Encryption and Decryption of the World War One ADFGVX Cipher, through examples. This video replaces an earlier one with the same content, but has some improvements and corrections. #cryptography
From playlist Classical Cryptography

The Langevin MCMC: Theory and Methods (Lecture 2) by Eric Moulines
PROGRAM: ADVANCES IN APPLIED PROBABILITY ORGANIZERS: Vivek Borkar, Sandeep Juneja, Kavita Ramanan, Devavrat Shah, and Piyush Srivastava DATE & TIME: 05 August 2019 to 17 August 2019 VENUE: Ramanujan Lecture Hall, ICTS Bangalore Applied probability has seen a revolutionary growth in resear
From playlist Advances in Applied Probability 2019

Follow-up: Barbie electronic typewriter
Here is a copy of the description from the Barbie video: ---- I first found this story on the crypto museum website, which has great information about the Barbie typewriter (and other cipher machines) https://www.cryptomuseum.com/crypto/mehano/barbie/ ------- Thanks to Sarah Everett fr
From playlist My Maths Videos

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

Toy Substitution Cipher 1 - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography