Random Oracle - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

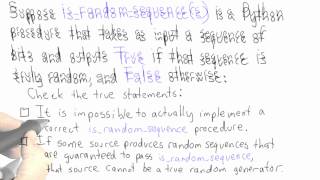
Questions And Answers - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
Randomness - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Dominique Unruh - The quantum random oracle model Part 1 of 2 - IPAM at UCLA
Recorded 28 July 2022. Dominique Unruh of Tartu State University presents "The quantum random oracle model I" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: The random oracle is a popular heuristic in classical security proofs that allows us to construct
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Dominique Unruh - The quantum random oracle model Part 2 of 2 - IPAM at UCLA
Recorded 28 July 2022. Dominique Unruh of Tartu State University presents "The quantum random oracle model II" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: The random oracle is a popular heuristic in classical security proofs that allows us to construct
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography
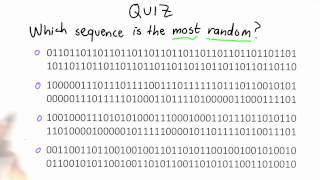
Randomness Quiz - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography

Random Oracle Solution - Applied Cryptography
This video is part of an online course, Applied Cryptography. Check out the course here: https://www.udacity.com/course/cs387.
From playlist Applied Cryptography
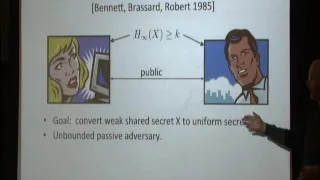
Randomness Extraction: A Survey - David Zuckerman
David Zuckerman University of Texas at Austin; Institute for Advanced Study February 7, 2012 A randomness extractor is an efficient algorithm which extracts high-quality randomness from a low-quality random source. Randomness extractors have important applications in a wide variety of area
From playlist Mathematics

Jonathan Katz - Introduction to Cryptography Part 2 of 3 - IPAM at UCLA
Recorded 25 July 2022. Jonathan Katz of the University of Maryland presents "Introduction to Cryptography II" at IPAM's Graduate Summer School Post-quantum and Quantum Cryptography. Abstract: This session will focus on public-key cryptography, including key exchange, public-key encryption,
From playlist 2022 Graduate Summer School on Post-quantum and Quantum Cryptography

Zero Knowledge Proofs - Seminar 4 - Non-interactive Zero Knowledge
This seminar series is about the mathematical foundations of cryptography. In this series Eleanor McMurtry is explaining Zero Knowledge Proofs (ZKPs). This seminar continues the development of non-interactive Zero Knowledge protocols, closing in on systems that can be used in practice. Yo
From playlist Metauni
Oracle Separation of Quantum Polynomial time and the Polynomial Hierarchy - Avishay Tal
Computer Science/Discrete Mathematics Seminar I Topic: Oracle Separation of Quantum Polynomial time and the Polynomial Hierarchy Speaker: Avishay Tal Affiliation: University of California, Berkeley Date: Oct 1, 2018 For more video please visit http://video.ias.edu
From playlist Mathematics

Zero Knowledge Proofs - Seminar 4 - From interactive to non-interactive
This seminar series is about the mathematical foundations of cryptography. In this series Eleanor McMurtry is explaining Zero Knowledge Proofs (ZKPs). This seminar explains how to construct *non-interactive* ZKPs which are much more practical than the schemes discussed so far in the semina
From playlist Metauni
Equality Alone Does not Simulate Randomness- Marc Vinyals
Computer Science/Discrete Mathematics Seminar I Topic: Equality Alone Does not Simulate Randomness Speaker: Marc Vinyals Affiliation: Technion Date: January 27, 2020 For more video please visit http://video.ias.edu
From playlist Mathematics

DEFCON 19: Speaking with Cryptographic Oracles
Speaker: Daniel Crowley Application Security Consultant, Trustwave - SpiderLabs Cryptography is often used to secure data, but few people have a solid understanding of cryptography. It is often said that if you are not strictly a cryptographer, you will get cryptography wrong. For that ma
From playlist DEFCON 19

Some Cryptographic Tools (in Blockchains) by Manoj Prabhakaran
DISCUSSION MEETING : FOUNDATIONAL ASPECTS OF BLOCKCHAIN TECHNOLOGY ORGANIZERS : Pandu Rangan Chandrasekaran DATE : 15 to 17 January 2020 VENUE : Madhava Lecture Hall, ICTS, Bangalore Blockchain technology is among one of the most influential disruptive technologies of the current decade.
From playlist Foundational Aspects of Blockchain Technology 2020

MIT MAS.S62 Cryptocurrency Engineering and Design, Spring 2018 Instructor: Tadge Dryja View the complete course: https://ocw.mit.edu/MAS-S62S18 YouTube Playlist: https://www.youtube.com/playlist?list=PLUl4u3cNGP61KHzhg3JIJdK08JLSlcLId Discreet log contracts including conditional payments,
From playlist MIT MAS.S62 Cryptocurrency Engineering and Design, Spring 2018
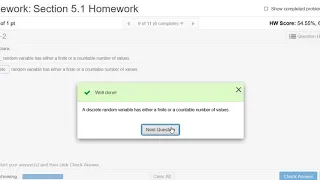
Conceptual Questions about Random Variables and Probability Distributions
Please Subscribe here, thank you!!! https://goo.gl/JQ8Nys Conceptual Questions about Random Variables and Probability Distributions
From playlist Statistics