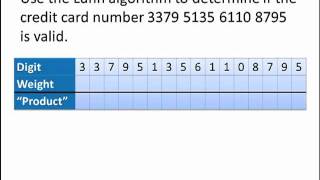
Math for Liberal Studies: The Luhn Algorithm
In this video, we learn how to use the Luhn algorithm to verify credit card ID numbers, and find missing check digits. For more information, visit the Math for Liberal Studies homepage: http://webspace.ship.edu/jehamb/mls/index.html
From playlist Math for Liberal Studies

Checksums: The Luhn Algorithm for Verifying Credit Card Numbers
The Luhn Algorithm is used to catch common input errors for credit card numbers: transposition or mistyping one or more digits. In this video I'll show you how to Luhn Algorithm works and why merchants want to catch these error before running the transaction.
From playlist Discrete Structures

Solve a System of Linear Equations Using LU Decomposition
This video explains how to use LU Decomposition to solve a system of linear equations. Site: http://mathispower4u.com Blog: http://mathispower4u.wordpress.com
From playlist Matrix Equations

Math for Liberal Studies - Lecture 3.3.2 ISBN's and Credit Card Numbers
This is the second video lecture for Math for Liberal Studies Section 3.3: More Check Digit Systems. In this video, we build on the idea of weighted sums from the previous video. We discuss two variations on that idea, applied to ISBN's (book identification numbers) and credit card numbers
From playlist Math for Liberal Studies Lectures

2-2 Solving by Multiplying and Dividing
From playlist Lufkin HS Algebra 1

LU Decomposition - Shortcut Method
This video explains how to find the LU Decomposition of a square matrix using a shortcut involving the opposite of multipliers used when performing row operations. Site: http://mathispower4u.com Blog: http://mathispower4u.wordpress.com
From playlist Matrix Equations

Discrete Structures: Random number generators, checksums, hashing
Learn about random number generators, checksums, and hashing. We'll start with the von Neumann random number generator and the contemporary linear congruential generator. Then we'll go over the Luhn algorithm used for credit card number validation and then introduce hash functions such as
From playlist Discrete Structures, Spring 2022
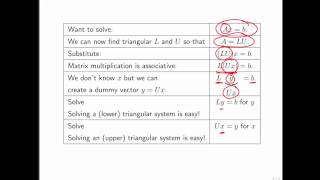
6.3.4 Solving A x = b via LU factorization, L y = b, and U x = y
6.3.4 Solving A x = b via LU factorization, L y = b, and U x = y
From playlist LAFF - Week 6
In LU decomposition we decompose a matrix into two matrices, that, when multiplied in a certain order, gives rise to the original matrix. L is a lower triangular matrix, and U is an upper triangular matrix. An upper triangular matrix has entries equaling zero below the main diagonal and a
From playlist Introducing linear algebra

Linear Algebra 13e: The LU Decomposition
https://bit.ly/PavelPatreon https://lem.ma/LA - Linear Algebra on Lemma http://bit.ly/ITCYTNew - Dr. Grinfeld's Tensor Calculus textbook https://lem.ma/prep - Complete SAT Math Prep
From playlist Part 1 Linear Algebra: An In-Depth Introduction with a Focus on Applications

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
logarithm of a matrix. I calculate ln of a matrix by finding the eigenvalues and eigenvectors of that matrix and by using diagonalization. It's a very powerful tool that allows us to find exponentials, sin, cos, and powers of a matrix and relates to Fibonacci numbers as well. This is a mus
From playlist Eigenvalues

Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security
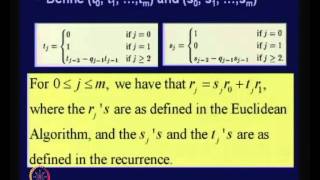
Cryptography and Network Security by Prof. D. Mukhopadhyay, Department of Computer Science and Engineering, IIT Kharagpur. For more details on NPTEL visit http://nptel.iitm.ac.in
From playlist Computer - Cryptography and Network Security

CSPs with Global Modular Constraints: Algorithms and Hardness via... - Sivakanth Gopi
Computer Science/Discrete Mathematics Seminar I Topic: CSPs with Global Modular Constraints: Algorithms and Hardness via Polynomial Representations Speaker: Sivakanth Gopi Affiliation: Microsoft Researcher Date: March 30, 2020 For more video please visit http://video.ias.edu
From playlist Mathematics

Hacking at Quantum Speed with Shor's Algorithm | Infinite Series
Viewers like you help make PBS (Thank you 😃) . Support your local PBS Member Station here: https://to.pbs.org/donateinfi Classical computers struggle to crack modern encryption. But quantum computers using Shor’s Algorithm make short work of RSA cryptography. Find out how. Tweet at us! @
From playlist Cryptography 101

Approximating the Longest Increasing Subsequence in Polylogarithmic Time - Michael Saks
Michael Saks Rutgers, The State University of New Jersey October 12, 2010 Finding the longest increasing subsequence (LIS) is a classic algorithmic problem. Simple O(nlogn)O(nlogn) algorithms, based on dynamic programming, are known for solving this problem exactly on arrays of length nn.
From playlist Mathematics

Factoring with Elliptic Curves - Jeremy Teitelbaum [2018]
May 30: Jeremy Teitelbaum (UConn) Title: Factoring with elliptic curves. Abstract: Lenstra’s elliptic curve algorithm ([1]) for factoring is a standard piece of the toolkit for computational number theory. I will give a brief introduction to this algorithm. [1] H. Lenstra, Factoring integ
From playlist Number Theory