
More videos like this online at http://www.theurbanpenguin.com We now look at how we can use and define methods in ruby to help keep the code tidy and concise. This also helps with readability of the code and later maintenance. In the example we use we take the decimal to ip address conver
From playlist RUBY

Dynamic Random Access Memory (DRAM). Part 3: Binary Decoders
This is the third in a series of computer science videos is about the fundamental principles of Dynamic Random Access Memory, DRAM, and the essential concepts of DRAM operation. This video covers the role of the row address decoder and the workings of generic binary decoders. It also expl
From playlist Random Access Memory

Cryptograph: Substitution Cipher (Caesar Cipher)
This lesson explains how to encrypt and decrypt a message using a Caeser cipher. Site: http://mathispower4u.com
From playlist Cryptography

Network Security: Classical Encryption Techniques
Fundamental concepts of encryption techniques are discussed. Symmetric Cipher Model Substitution Techniques Transposition Techniques Product Ciphers Steganography
From playlist Network Security
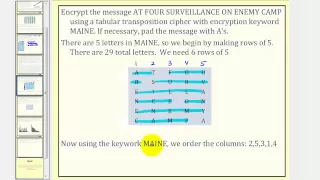
Cryptography: Transposition Cipher
This lesson explains how to encrypt and decrypt a message using a transposition cipher. Site: http://mathispower4u.com
From playlist Cryptography
Find all the solutions of trig equation with cotangent
👉 Learn how to solve trigonometric equations. There are various methods that can be used to evaluate trigonometric equations, they include by factoring out the GCF and simplifying the factored equation. Another method is to use a trigonometric identity to reduce and then simplify the given
From playlist Solve Trigonometric Equations
Solving a trigonometric equation with applying pythagorean identity
👉 Learn how to solve trigonometric equations. There are various methods that can be used to evaluate trigonometric equations, they include factoring out the GCF and simplifying the factored equation. Another method is to use a trigonometric identity to reduce and then simplify the given eq
From playlist Solve Trigonometric Equations by Factoring

How to find all of the solutions to an equation as well as within the unit circle
👉 Learn how to solve trigonometric equations. There are various methods that can be used to evaluate trigonometric identities, they include by factoring out the GCF and simplifying the factored equation. Another method is to use a trigonometric identity to reduce and then simplify the give
From playlist Solve Trigonometric Equations

How-to Decode Outputs From NLP Models (Python)
In this video, we will cover three ways to decode the output probabilities from NLP models - greedy search, random sampling, and beam search. Learning how to decode outputs can make a huge difference in diagnosing model issues and improving text output quality - and as an added bonus it's
From playlist Recommended
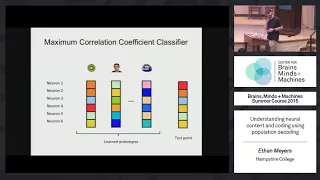
Tutorial 4: Ethan Meyers - Understanding Neural Content via Population Decoding
MIT RES.9-003 Brains, Minds and Machines Summer Course, Summer 2015 View the complete course: https://ocw.mit.edu/RES-9-003SU15 Instructor: Ethan Meyers Population decoding is a powerful way to analyze neural data - from single cell recordings, fMRI, MEG, EEG, etc - to understand the info
From playlist MIT RES.9-003 Brains, Minds and Machines Summer Course, Summer 2015

Structured Neural Summarization | AISC Lunch & Learn
For more details including paper and slides, visit https://aisc.a-i.science/events/2019-04-16/ Abstract Summarization of long sequences into a concise statement is a core problem in natural language processing, requiring non-trivial understanding of the input. Based on the promising re
From playlist Natural Language Processing
0005 - Developing a web service framework from scratch
This is #5 in my series of live (Twitch) coding streams, working on writing my own web server and service framework in C++. Continuing development on URI parser -- fixed a few things I realized were wrong in the design so far, and did a bit more refactoring -- Watch live at https://www.tw
From playlist Excalibur

Learn low-dim Embeddings that encode GRAPH structure (data) : "Representation Learning" /arXiv
Optimize your complex Graph Data before applying Neural Network predictions. Automatically learn to encode graph structure into low-dimensional embeddings, using techniques based on deep learning and nonlinear dimensionality reduction. An encoder-decoder perspective, random walk approach
From playlist Learn Graph Neural Networks: code, examples and theory

Multilingualism in Natural Language Processing targeting low resource languages by Sudeshna Sarkar
DISCUSSION MEETING THE THEORETICAL BASIS OF MACHINE LEARNING (ML) ORGANIZERS: Chiranjib Bhattacharya, Sunita Sarawagi, Ravi Sundaram and SVN Vishwanathan DATE : 27 December 2018 to 29 December 2018 VENUE : Ramanujan Lecture Hall, ICTS, Bangalore ML (Machine Learning) has enjoyed tr
From playlist The Theoretical Basis of Machine Learning 2018 (ML)

VQ-GAN | PyTorch Implementation
In this video we are implementing the famous Vector Quantized Generative Adversarial Networks (VQGAN) paper using PyTorch. VQGAN is a generative model for image modeling. It was introduced in Taming Transformers for High-Resolution Image Synthesis. The concept is build upon two stages. The
From playlist Paper Implementations

From playlist fastai v2 code walk-thrus
Deep Decoder: Concise Image Representations from Untrained Networks (Lecture 2) by Paul Hand
DISCUSSION MEETING THE THEORETICAL BASIS OF MACHINE LEARNING (ML) ORGANIZERS: Chiranjib Bhattacharya, Sunita Sarawagi, Ravi Sundaram and SVN Vishwanathan DATE : 27 December 2018 to 29 December 2018 VENUE : Ramanujan Lecture Hall, ICTS, Bangalore ML (Machine Learning) has enjoyed tr
From playlist The Theoretical Basis of Machine Learning 2018 (ML)
Mathieu Bouvier Des Noes - Sécurité des communications par étalement de spectre
Sécurité des communications par étalement de spectre
From playlist Journées Codage et Cryptographie 2014

How to find all of the solutions of an equation with secant
👉 Learn how to solve trigonometric equations. There are various methods that can be used to evaluate trigonometric identities, they include by factoring out the GCF and simplifying the factored equation. Another method is to use a trigonometric identity to reduce and then simplify the give
From playlist Solve Trigonometric Equations
